CMS Security: How to Maintain a Highly Secure Website

Why CMS Security Risk Analysis Is Important
In the late twenty-teens, a hacking epidemic struck the United States. When the city of Riviera Beach, Florida found that its 911 emergency system had been compromised, officials paid hackers hundreds of thousands of dollars in cryptocurrency to bring it back online. The city of Atlanta was attacked as well, by another group of hackers, but refused to pay a ransom.
Security breaches weren’t limited to municipalities. The band Radiohead was asked for $150,000 in return for keeping an unreleased, stolen album withheld from the public. The band decided to release the album for free instead of paying the money. Many other cases emerged around the same time. The attacks were a wake-up call. Security had been neglected and we were paying the price.
Since 2018, many businesses, cities, and organizations have stepped up to meet modern security challenges. Though, the state of security is ever-evolving. A fix is never permanent. Website and CMS security need to be audited and updated regularly.
Common CMS Security Concerns
For many developers, a website’s content management system (CMS) is of particular concern in terms of security. There are many ways the CMS can cause weaknesses.
Code Injection involves the insertion (or injection) of extra code into a website, often with unwanted results. SQL injection is one of the most common cyberattacks.
Cross-Site Scripting (XSS) is another type of injection attack where the code is executed from a browser instead of the CMS or website files. Several coding languages are susceptible to XSS attacks.
Session Management attacks occur when attackers gain the privileges of a legitimate site visitor by taking control of a session token. The illegitimate visitor can then make purchases, gain access to sensitive information, or carry out other unwanted actions.
Cross-Site Request Forgeries trick site visitors into submitting an unintended request, which can cause data leakage, account manipulation, or other problems.
Is My Site a Desirable Target for Hackers?
There are a plethora of reasons attackers may hack a site. If a site has any of the following characteristics, it might be more likely to incur an attack than others.
- Access to personal information such as phone numbers and email addresses, which can be used for phishing, scamming, and spamming.
- Access to credit card numbers, bitcoin, and other currencies.
- High traffic volume, which makes a site desirable for setting up links to malicious sites.
- Top-ranked content and high-traffic pages. “SEO spam” happens when attackers redirect traffic from one website to another by adding hyperlinks and keywords to high-performance pages. This can lead to severe SEO penalties and even blacklisting by search engines.
- Sensitive, political, or contentious content sometimes makes a site attractive to “hacktivists” who disagree with the ideology of it. Distributed Denial of service (DDoS) attacks can render a site inaccessible.
Another source of cyberattacks, sadly, is boredom. Just about any cyber vandal can access pre-written scripts designed to bring a website down. Sometimes it’s for no reason other than a desire to cause trouble. That means even a site with no valuable or personal information might be a target. Webmasters of such sites should stay safe just as others should. Preventing an attack, at least, could mean there’s no need to rebuild it or re-setup.
Why Is CMS Security So Vulnerable?
A site’s lack of security is often blamed on its CMS for several reasons. Two of the most popular CMS’s, WordPress and Drupal, are open-source. That means they can be easily modified to suit a wide range of needs. At the same time, though, it means there’s nobody directly accountable for the security of the platform. Any security initiatives of open-source software creators can be considered charitable. They rarely address specific security issues a business might have. Instead, they sometimes attempt to address a range of common concerns with upcoming versions. Sometimes this leaves hackers an open door that can cause some damage.
Besides that systemic issue, the CMS is often a security risk because it provides different means by which attackers can strike, such as plugins and separate login credentials.
It’s a little counterintuitive, but open-source systems are considered more secure than closed-source systems if upgraded on time. That’s because new versions are available quickly and consistently. Proprietary (closed-source) CMS applications can be as secure as their open-source counterparts but it’s important to choose a reputable one.
Which CMS Is Most at Risk of Cyberattacks?
A common comparison to make is Drupal vs WordPress. Drupal is considered more secure than WordPress for most websites since it doesn’t rely on third-party plugins as much as WordPress does. Luckily, WordPress’s plugin concern is easy to fix. Just keep the site and its plugins up-to-date to resolve most security issues.
A 2018 study of 25,466 infected websites by Sucuri shows that 90% of the infected websites brought to the company’s attention were running on WordPress. This statistic has been heavily shared across the internet but it isn’t very useful. The study states that the figure “reflects the overall popularity of [each] CMS.” In other words, 90% of the breaches and infections brought to Sucuri’s attention were on WordPress sites because it's a very popular CMS. Their sample included only infected sites, so they can’t determine the infection rate of each CMS.
See our in-depth Drupal vs WordPress comparison.
Which CMS Has the Best Security Track Record?

Even if we had a reliable study about CMS infection rates or some kind of vulnerability rating, it wouldn’t be as useful as one would think. Every website needs to be audited and updated regularly. Any site can become unsecure for numerous reasons and each has different kinds of assets to protect. Platforms are being updated regularly and each update can solve a lot of problems. So, it’s not always a good idea to choose a CMS based on statistical figures found online.
No matter what, every organization should take precautions to keep their websites secure. The question of website and CMS security should be revisited regularly. Actions should be taken if a weakness is noticed or if one is expected to show up in the near future. For sites that have access to sensitive information, a CMS audit or website security audit should be performed by a professional web development agency such as O8 when internal resources are not sufficient.
Drupal users, is it time to upgrade to a newer version?
How to Make a Website Secure (5 Tasks)
Every website has unique security concerns and requirements. Some actions can reduce security risk for all kinds of sites, however. These exclude obvious chores like backing up the CMS and database often and deleting default admin usernames. Don’t forget those!
1. Subscribe for Informative Updates
The rapidly changing nature of technology means professionals need to study frequently to stay “in the know.” When they don’t, they risk costly oversight. WPScan’s Vulnerability Database is a great resource for webmasters using WordPress. Sign up for email alerts and get informed when important news happens. Drupal users can get security updates by navigating to the user profile page, looking under “edit” and then clicking the “my newsletters” tab.
2. Update the CMS and Plugins and Audit Regularly
Updating (or patching) a CMS reduces security risk by resolving common issues. It’s a good idea to update regularly. It’s equally as important to update and audit the plugins used with any CMS, but especially with WordPress. Check to make sure plugins are up to date. Also, make sure they have had updates issued fairly recently. If the latest version is years old, it might be a risk to continue using it. Any plugins with few reviews, bad reviews, or a low installation count could be risky as well. Use reputable plugins when possible.
3. Use a CDN
Content distribution networks (CDNs) like Cloudflare are networks of servers that speed websites up. Visitors connect to the CDN instead of the site’s server, which results in better security most of the time. Most CDNs provide a range of additional security features as well. For more information about CDNs and how they give us peace of mind, see our blog post here.
4. Watch Out for PHP
For CMS’s that use PHP as the underlying programming language, it’s important to always use the most up-to-date version of PHP and block the execution of PHP files in sensitive directories like “wp-includes” and “uploads.” This can fend off hackers who use backdoor access files to gain control of websites.
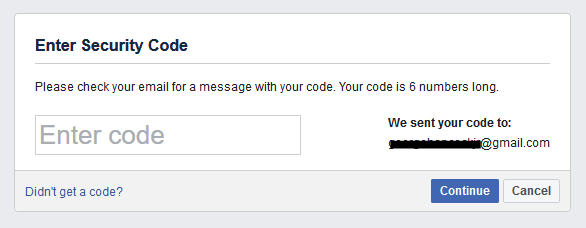
5. Set Up 2FA
Two-factor authentication (2FA) or multi-factor authentication is always a good idea. An example of 2FA is requiring the user to receive a code by text message or email and then enter it when logging in, to prove their identity. Facebook requires 2FA when a user hasn’t logged in with a specific browser for a while.
Following the advice above should prevent most breaches. If there’s any suspicion or if any of the tasks above haven’t been completed promptly, review the site’s analytics in Google Search Console. Any downtime or slowdowns may be due to a cyberattack.
The Future of CMS Security
What about 2021 and beyond? What threats are coming? Will new CMS versions be more secure than the current ones?
It’s always difficult to predict what’s ahead in the technology business. What we know for sure is that outdated CMS versions will have more and more security risks as they age. We also know that innovative new malware is on the way. There’s no cyber-attack-free era in sight, sadly.
Single sign-on (SSO) allows users to sign into multiple software systems with a single set of login credentials. SSO and 2-factor authentication (2FA) will become increasingly mainstream over the next few years, with 2FA becoming common practice soon. Jumping on the bandwagon early won’t hurt!
Business leaders who don’t have the resources or know-how to manage CMS security properly can always get in touch with a web dev agency like O8 to get an audit. Many organizations find the cost benefits of a remote fractional team attractive and convenient when in-house web dev can’t hit the mark

